

Gain The Decisive Adventage
See across your terrain to detect, hunt and respond to threats and protect your data.
Gain The Decisive Adventage
See across your terrain to detect, hunt and respond to threats and protect your data.
Product




















Open XDR is Everything Detection & Response

Stellar Cyber is the only security operations platform providing high-speed high-fidelity threat detection across the entire attack surface
Stellar Cyber Open XDR is a unified, AI-powered approach to detection and response, that collects and correlates all existing security tools, to protect the entire enterprise attack surface effectively and efficiently. Open XDR is Everything Detection and Response, more than eXtended Detection and Response, because it must defend against all threats across the entire attack surface. The only way to do this is by integrating with existing security tools.
Architecturally, Open XDR is about unifying and simplifying the entire Security Stack for the purpose of radically improving detection and response. At any given enterprise, a Security Stack will consist of numerous capabilities like SIEM, EDR, NDR, SOAR and more. These capabilities were never designed to work with each other, and teams spend too much time managing multiple tools, which is what leads to the problems of today – too many tools, not enough people, not right data. That’s where Open XDR comes in.
Privileged Access Management (PAM) and Access Management (IAM)

Kron produces high technology solutions for the operational efficiency and security needs of corporate enterprises in finance, energy and health sectors, particularly in telecommunications.
Privileged Access Management (PAM) is a cybersecurity domain within Identity and Access Management (IAM) that focuses on monitoring and controlling privileged users and privileged accounts within an organization.
Krontech’s Single Connect™ product family strengthens, simplifies and secures the management of privileged accounts, for enterprises and network operators who serve them. Single Connect™ unifies multivendor environments with pre-integrated modules managing dozens of vendors and hundreds of network elements and servers with a single, universal system.
Privileged Session Manager
Secures privileged users (IT and Network admins) access to critical systems. Tracks all user activities and provides VCR-like replays of sessions. Prevents unsupervised access by inside actors, contractors or 3rd parties to critical systems.
Two-Factor Authentication
Provides second layer of security to verify your identity to make fraud attempts ineffective.
Unified Access Manager
Provides AAA services for network infrastructure and extends authentication and policy configurations of AD to network.
Data Access Manager & Dynamic Data Masking
Single point of access control management for database layer, secures data access with logging, policy enforcement, and masking.
Cloud PAM
Protects client organizations’ assets whether their infrastructure is on-premise, cloud or hybrid, and supports Cloud IaaS platforms.
Privileged Task Automation
Provides a single interface to configure the ability of network business flows with dynamic and extendable command sets.
Discover your attack surface with SOCRadar’s External Attack Surface Management

Organizations need to have better visibility into external facing assets and services and the related vulnerabilities they may present.
It is clearly not sufficient to have only EASM solutions to eliminate cyber risks. Rather, EASM technologies are advised to be a component of a broader enterprise vulnerability management strategy.
Protect your digital assets with SOCRadar’s Digital Risk Protection Services
Enterprises are seeking digital asset protection wherever exposure may occur. The traditional focus on social media and the dark web is insufficient as threat actors proliferate sources.
Monitoring capabilities across all environments (cloud buckets, dark web) are considered to equip the security team effectively. For a comprehensive Digital Risk Protection, services like site takedown and automated remediation should also be included. With a full-fledged DRPS , your organization will be more resilient against DDoS attacks.
Early warning system against cyber threats
SOCRadar XTI offers monitoring services for dark web and other sources for potential threats targeting organizations, detecting impersonating domains, tracking social media platforms for brand abuse alerting companies to potential threats before they could cause damage.
Automated Security Validation & Breach and Attack Simulation Platform

Picus Security is an Automated Security Validation platform that helps organizations continuously test and measure the effectiveness of their cybersecurity defenses through realistic cyberattack simulations.
As cyber threats continue to evolve, organizations need more than just security tools—they need to ensure that their existing defenses are capable of detecting and stopping real-world attacks. Picus Security addresses this challenge by providing a comprehensive Breach and Attack Simulation (BAS) platform that allows organizations to safely simulate thousands of cyberattack scenarios across their infrastructure.
The platform continuously validates security controls by emulating attacker techniques based on widely recognized threat frameworks such as MITRE ATT&CK. Through these simulations, security teams can observe how their security stack—including firewalls, endpoint protection platforms, intrusion detection systems, SIEM solutions, and other defensive technologies—responds to different types of attacks.
Picus also provides detailed reporting and actionable recommendations that help organizations identify misconfigurations, security gaps, and detection failures. These insights allow security teams to prioritize remediation efforts and optimize the performance of their security controls.
By automating the process of security validation, Picus enables organizations to adopt a proactive security strategy. Instead of waiting for an actual breach to expose weaknesses, organizations can continuously test and improve their defenses, strengthen their cyber resilience, and ensure their security investments are delivering real protection.
Maximise Your Investment in Monitoring and Security Tools With Network Packet Broker

Networks have become increasingly complex due to the adoption of transformational technologies including 5G SA, SDN, SD-WAN, virtualization, and IoT. This has created ‘blind spots’.
Blind spots are network traffic that is not visible to network monitoring, security and analytics tools and can hide and obscure network performance and security threats.
What is the role of a network packet broker?
Network Packet Brokers (NPBs) remove network traffic blind spots, optimize network traffic, filter network traffic, load balance, and support high speed connections (currently) up to 400Gbps. NPBs receive and aggregate network traffic from switch SPAN ports or network TAPs which can then be filtered, deduplicated, and further optimized to enable more efficient use of security and performance tools.
What makes Cubro’s network packet broker different?
Cubro’s advanced NPBs are designed to meet the needs of complex networks and support numerous tunnelling protocols including MPLS, MPLS over UDP, GRE, NVGRE, VXLAN, CFP, ERSPAN and GTP. The key to realizing such an advanced feature set is that we are using high-performance silicons giving us the flexibility and performance to truly function as a Next Generation Network Packet Broker.
Passwordless Authentication & Digital Identity Verification Platform

1Kosmos is a passwordless authentication and digital identity verification platform that enables secure user access without relying on traditional passwords.
Passwords have long been considered one of the weakest links in cybersecurity. Weak credentials, password reuse, and phishing attacks continue to be major causes of security breaches across organizations. 1Kosmos addresses these challenges by eliminating the need for passwords and replacing them with a secure, identity-based authentication approach.
The platform combines biometric authentication, AI-powered identity verification, and decentralized identity technology to ensure that users accessing systems and applications are properly verified. Instead of relying on passwords, users can authenticate themselves using biometric verification through their trusted devices, creating a faster and more secure login experience.
1Kosmos is designed to integrate seamlessly with existing enterprise infrastructure, including Identity and Access Management (IAM) systems, cloud services, and enterprise applications. This allows organizations to deploy passwordless authentication without requiring significant changes to their existing systems.
In addition to improving security, the platform also enhances user experience by simplifying the authentication process. Users no longer need to remember complex passwords or manage multiple credentials across different systems.
By implementing passwordless authentication and digital identity verification, organizations can significantly reduce the risk of credential-based attacks, strengthen access security, and create a more seamless and secure digital identity experience.
Endpoint Privilege Management & Secure Admin Access

Admin By Request is an Endpoint Privilege Management solution that allows organizations to control and secure administrator access on endpoint devices.
In many organizations, users are often granted permanent administrator privileges on their devices to perform daily tasks. While convenient, this practice significantly increases the risk of security incidents, as malicious software or attackers can exploit elevated privileges to gain deeper access into systems.
Admin By Request addresses this issue by removing permanent administrator rights and replacing them with a controlled privilege elevation model. Users operate with standard permissions by default and can request temporary administrative access only when it is required to complete a specific task.
These privilege requests can be automatically approved based on predefined policies or reviewed by IT administrators before being granted. This approach ensures that elevated privileges are used only when necessary and under proper supervision.
The platform also provides extensive visibility through audit logs, activity tracking, and session recording, enabling organizations to monitor administrative actions performed on endpoints. This visibility helps security teams maintain compliance with security policies and regulatory requirements.
By implementing controlled privilege management, Admin By Request helps organizations reduce the attack surface on endpoints, prevent unauthorized system changes, and protect critical systems from privilege-based attacks.
Where Security Meets Peace of Mind
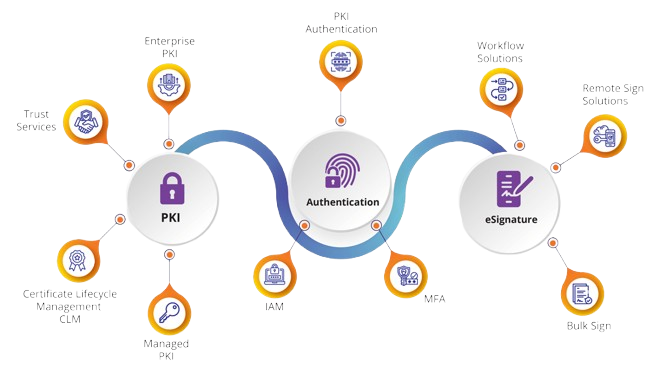

eMudhra was started in 2008 with a mission to accelerate the world’s transition to a secure integrated digital society with a foundation built on digital identity and trust.
eMudhra is a leading provider of digital trust services, specializing in digital signatures, identity management, and secure digital transformation solutions. The company plays a crucial role in enabling organizations and individuals to conduct secure, paperless transactions in both private and public sectors.
At the core of eMudhra’s offerings is its Digital Signature Certificate (DSC) service, which ensures the authenticity and integrity of digital documents. eMudhra also provides eSign services, allowing users to sign documents remotely through a cloud-based infrastructure, removing the need for physical tokens or hardware.
Beyond signatures, eMudhra offers comprehensive Identity and Access Management (IAM) solutions that help organizations manage user identities, enforce authentication policies, and ensure role-based access to digital systems. This is especially critical for enterprises looking to enhance cybersecurity while maintaining regulatory compliance.
The company’s Public Key Infrastructure (PKI) services form the foundation for many of its products, enabling encryption, digital signing, and secure communication across networks. It supports a range of compliance standards including GDPR, HIPAA, and other global cybersecurity frameworks.
eMudhra also enables businesses to transition to paperless environments, providing digital workflow tools, document management systems, and automated approval processes. These solutions help reduce operational costs, boost efficiency, and support sustainability initiatives.
With a strong focus on innovation and compliance, eMudhra serves sectors such as banking, healthcare, government, and enterprises by delivering trust and security in the digital world.
Privileged Access Service

According to Forrester, 80 percent of all hacking-related data breaches involve privileged access credentials. This illustrates that the legacy approach to Privileged Access Management is no longer enough and requires a rethinking of how to protect against privileged access abuse in today’s dynamic threatscape.
Centrify is redefining the legacy approach to Privileged Access Management (PAM) by delivering cloud-ready Zero Trust Privilege to secure access to infrastructure, DevOps, cloud, containers, Big Data and other modern enterprise use cases.
A New Approach to Privileged Access Management is Needed. As traditional network perimeters dissolve, organizations must discard the old model of “trust but verify” which relied on well-defined boundaries. Zero Trust mandates a “never trust, always verify, enforce least privilege” approach to privileged access, from inside or outside the network.
Organizations may consider approaching Privileged Access Management (PAM) by solely implementing password vaults, leaving gaps that can easily be exploited. Centrify Zero Trust Privilege combines password vaulting with brokering of identities, multi-factor authentication enforcement and “just enough” privilege, all while securing remote access and monitoring of all privileged sessions.
Redefining the Legacy Approach to Privileged Access Management
Centrify is redefining the legacy approach to Privileged Access Management (PAM) by delivering cloud-ready Zero Trust Privilege to secure access to infrastructure, DevOps, cloud, containers, Big Data and other modern enterprise use cases.
Centrify Zero Trust Privilege helps customers grant least privilege access based on verifying who is requesting access, the context of the request, and the risk of the access environment. By implementing least privilege access, Centrify minimizes the attack surface, improves audit and compliance visibility, and reduces risk, complexity and costs for the modern, hybrid enterprise.
- Over half of the Fortune 100, the world’s largest financial institutions, intelligence agencies, and critical infrastructure companies, all trust Centrify to stop the leading cause of breaches — privileged credential abuse.
Extended Detection and Response

Fidelis helps you outperform, outmaneuver and outfight cyber attackers at every step to keep your business operations and data safe. Enterprises are at a disadvantage against their cyber adversaries.
Threats come from every angle and many organizations lack complete visibility of their cyber terrain, allowing cyber attackers to lurk undetected as they take aim at sensitive data or look to disrupt business operations. To gain the decisive advantage, security teams need to think like their adversary.This means having greater visibility across the different layers within their environment as well as the automation to scale detection and response capabilities.
Developed and Used by Cyber Warriors
Fidelis Cybersecurity was founded by cyber warriors and continues that rich heritage today. Our cyber warriors are incident responders, SOC operators, intel analysts and threat hunters, from the DoD and US Intel Communities as well as Industry. Our team has built some of the most secure environments and has been called in post-breach to lead the incident response programs for some of the largest data breaches on record.
- Our platform provides cyber warriors with the ability to operate inside the adversary’s decision cycle and detect and respond to advanced threats at line speed. Not only do we develop the tools to help win the cyber battle, we use them on behalf of our customers – finding known and unknown threats, rooting them out and protecting sensitive data.
Title Title Title Title Title Title Title

The open visibility platform enables agile security deployment to keep ahead of attacker innovation and advancements.
Niagara’s NPB (Network Packet Brokers) deliver access to network data to NetOps & SecOps to enable detection, investigation and response to threats in real-time. Niagara’s NPB solutions are empowered by comprehensive Technology Alliance Program with world-class technology leaders and deployed in the world’s most prominent networks.
Fusion Platform

OCTOPUS Systems was founded in 2013 by a team of experienced security and technology experts with the mission of creating a new breed of smart, agile, and easy to deploy Command and Control software system. OCTOPUS’ advanced, Cloud-enabled Physical Security Information Management (PSIM) system and mobile application is offering customer solutions for a variety of vertical markets.
As a unified and converged platform, the OCTOPUS system integrates technology, procedures, and personnel into one command and control center, enabling you to effectively manage all security operations from one screen.
The OCTOPUS system helps organizations across the globe protect people, information, and assets, while constantly striving to raise the bar in the security industry.
See how the Octopus PSIM solution allows organizations to efficiently manage all physical security and cyber security incident and threats from one holistic system with a smart command and control engine combined with a rich mobile application platform.
The PSIM (Physical Security Information Management) is an advanced and innovative system for command-and-control of all the information security, safety, and building management and operations, for large enterprises with critical facilities, all handled from a single location via an advanced user interface, in a unified, secure and encrypted manner.
The Octopus System offers a One-stop shop for a security management system that incorporates all the software modules in a single location, currently developed or sold individually on the market. The System is flexible and based on an open architecture with advanced algorithms for connecting third-party Systems and components, and employs a highly advanced user-friendly interface, together with a rich set of apps for mobile devices, all securely managed.
The proposed system is currently in use in critical facilities and in large enterprises throughout Israel and worldwide, including in government ministries, smart cities, police forces, armies, major banks, energy firms, ports, security companies, communications companies, smart building management companies, etc.
Reliable and user-friendly, all our solutions are created internally and designed to be scalable and easy to customize according to your needs. The fact that we always design them in an innovative way, and their presence throughout the whole world are guarantees of our efficiency.
Since we believe in the convergence of technologies, we offer you the possibility to obtain a holistic view of your cybersecurity thanks to the Octopus Open Platform, allowing you to stop threats and adapt your strategies of today and tomorrow.
- PSIM Solutions
- Cyber Event Management
- Visitor Management
- Safety Management
- Performance And Monitoring
- Fleet Management
With Octopus, you’ll be ready. Ready to face the unpredictable.

